🧰 Online Validators, Linters, Generators, and Visual Tools for AppSec and DevSecOps
Intro: Security teams lose time when every quick check requires a local lab or a giant platform. This page collects high-signal tools that help you validate, lint, generate, visualize, or prototype security-relevant artifacts faster. It intentionally mixes browser-based tools, local/CI-first OSS, cloud-native GUI builders, and a few commercial accelerators.
Safety rule: do not paste secrets, production tokens, customer data, proprietary configs, or private certificates into public browser tools. Use sanitized samples or local/self-hosted equivalents for sensitive material.
How to use this page
Use this page in three modes:
- Quick triage — validate syntax or policy logic before opening a big ticket.
- Authoring acceleration — generate or prototype YAML, policies, rules, and diagrams faster.
- Shift-left integration — once a quick browser test is useful, replace it with a local or CI-integrated workflow where possible.
Browser-based quick checks
| Tool | Best for | Why it is useful | Notes |
|---|---|---|---|
YAML Lint (yamllint.com) |
YAML syntax and basic formatting checks | fast feedback for malformed YAML before deeper tooling | good for quick sanity checks only |
JSONLint (jsonlint.com) |
JSON syntax and reformatting | useful for IAM policies, OpenAPI fragments, and rule payloads | avoid pasting sensitive JSON into public tools |
Swagger Editor (editor.swagger.io) |
OpenAPI editing and validation | quick browser-side way to validate and preview API contracts | excellent for fast contract debugging |
ValidKube (validkube.com) |
Kubernetes YAML validation and hygiene checks | wraps multiple OSS validators and scanners behind one browser UI | good first-pass tool for manifests |
Network Policy Editor (editor.networkpolicy.io) |
generate and visualize Kubernetes NetworkPolicy |
much faster than hand-writing policies from memory | especially useful for newcomers |
Kyverno Playground (playground.kyverno.io) |
prototype Kyverno policies in the browser | fast for validate/mutate/generate policy experiments | great for training and small proofs of concept |
OPA / Rego Playground (play.openpolicyagent.org) |
prototype Rego rules and inputs | ideal for policy logic debugging and sharing examples | works beyond Kubernetes too |
Falco Playground (play.falco.org) |
author and validate Falco rules | helps tune runtime-detection logic without a full cluster | useful for learning rule structure |
CSP Evaluator (csp-evaluator.withgoogle.com) |
Content-Security-Policy review | catches weak CSP patterns and likely bypasses | very useful during frontend and edge reviews |
MDN HTTP Observatory (developer.mozilla.org/en-US/observatory) |
HTTP header posture review | fast header and TLS-adjacent posture feedback | good for public web surfaces |
SecurityHeaders (securityheaders.com) |
external header scan | fast external signal for headers such as HSTS and CSP | good as a second opinion, not a full review |
jwt.io (jwt.io) |
JWT decode / verify / generate | quick analysis of token structure and signing assumptions | never paste live secrets unless you accept the risk |
Mermaid Live Editor (mermaid.live) |
diagrams as code | excellent for architecture reviews, attack flows, and learning pages | useful for GitBook-friendly visuals too |
Real UI examples — browser and platform views
These screenshots are here for orientation, not as authoritative product documentation. They make the page easier to scan when you want to understand what a tool roughly looks like before opening it yourself. Interfaces change over time, so treat them as visual anchors rather than permanent truth.
YAML Lint — fast YAML sanity check
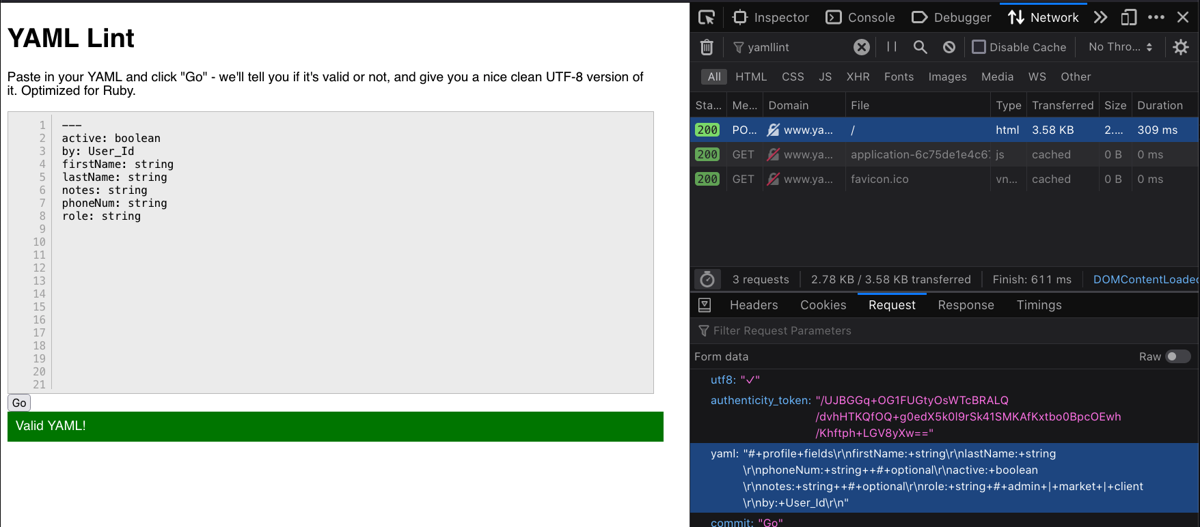
Public example screenshot of the YAML Lint web interface. Useful for quick syntax sanity checks before switching to CI-grade validation and policy tooling.
Swagger Editor — OpenAPI editing and validation in the browser
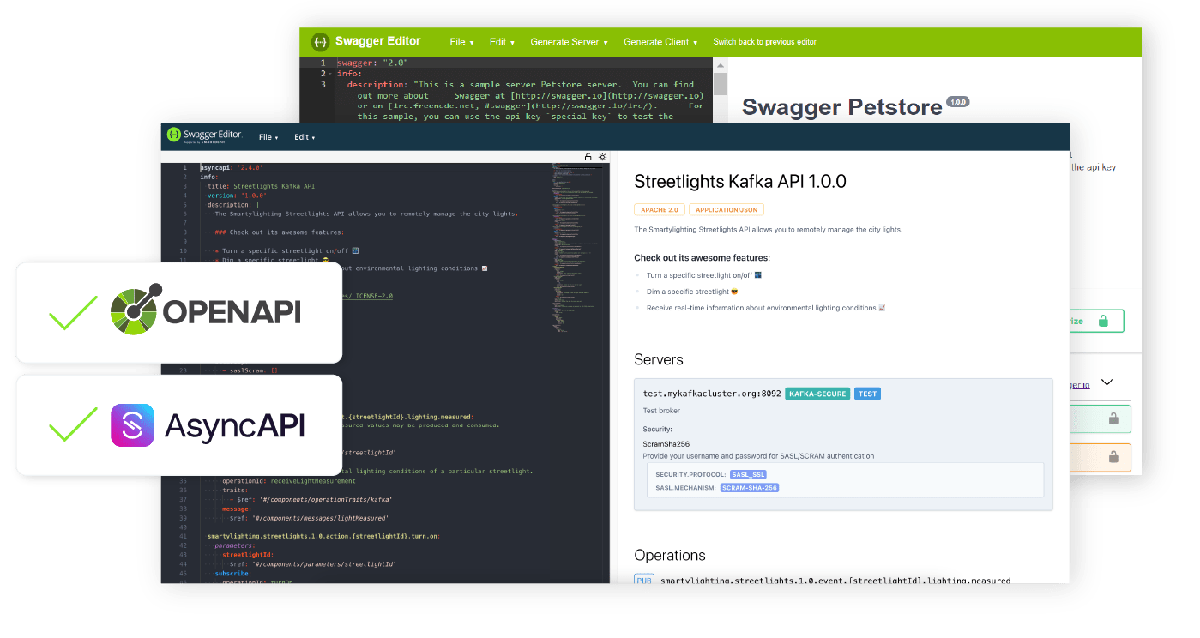
Public product screenshot showing the editor and live rendered documentation view side by side — exactly the kind of fast feedback loop that makes Swagger Editor useful during API design and contract review.
ValidKube — browser-first Kubernetes YAML validation
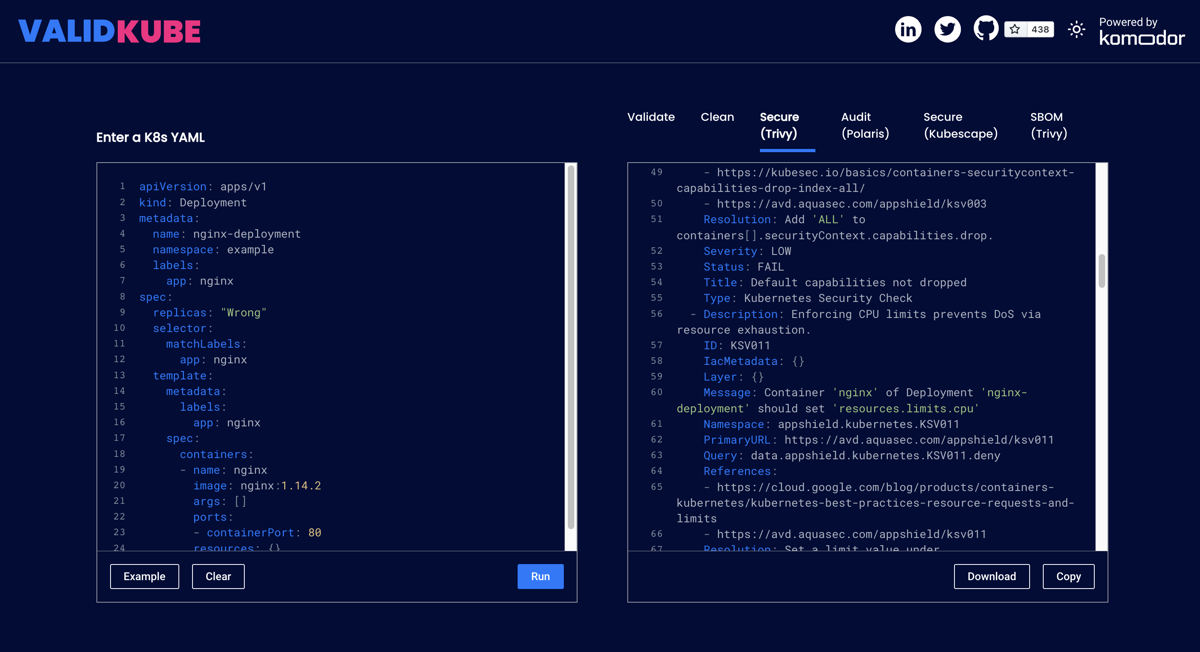
Public screenshot of ValidKube showing the split between raw manifest input and multi-tool analysis output. This is a good visual reminder that ValidKube is most useful as a quick first-pass manifest triage tool.
Local or CI-first validators and linters
These are better long-term choices once you move from exploration to repeatable control.
| Tool | Best for | Why it belongs in a serious workflow |
|---|---|---|
| Hadolint | Dockerfile linting | catches Dockerfile anti-patterns and even lints shell in RUN blocks |
| Redocly CLI | OpenAPI linting and bundling | strong for API lifecycle workflows and rule-driven linting |
| Spectral | OpenAPI / AsyncAPI / JSON/YAML linting | flexible rulesets for style, consistency, and security expectations |
| Checkov | IaC and cloud misconfiguration scanning | broad coverage across Terraform, Kubernetes, CI/CD, and more |
| Kubeconform | Kubernetes schema validation | very fast manifest validation and good CI fit |
| Polaris | Kubernetes best-practice validation | useful when you want policy checks plus dashboard/admission patterns |
| Trivy | vulnerabilities, misconfigurations, secrets, and SBOMs | broad scanner for containers, repos, IaC, and Kubernetes targets |
Policy playgrounds and generators
These are especially useful when the team understands the goal but does not want to hand-author raw policy from scratch.
| Tool / pattern | Use it for | Practical note |
|---|---|---|
| Network Policy Editor | build Kubernetes network policies visually | best first stop when you need a clean starter policy |
| Kyverno Playground | test validate/mutate/generate Kubernetes policies | good for policy design reviews and demos |
| OPA Playground | test Rego logic for admission, CI, or API policy | ideal for policy-as-code workshops |
| Falco Playground | build runtime-detection rules | useful before moving rules into Git and CI |
| AWS IAM Visual Editor | create IAM policies without hand-writing JSON | helpful for least-privilege starter policies |
| AWS IAM Access Analyzer policy generation | derive narrower IAM policies from CloudTrail activity | strong for reducing over-broad permissions after observing real use |
Cloud-native visual builders and managed GUIs
Not everything needs to start in a text editor. These provider-native experiences are often the fastest route to a safe baseline.
| Provider feature | Why it matters |
|---|---|
| AWS IAM Visual Editor | reduces raw-JSON authoring mistakes when creating policies |
| AWS IAM Access Analyzer | helps generate tighter policies from observed access activity |
| AWS WAF console / web ACL wizard | fast way to assemble rule groups, rate limits, logging, and associations |
| Azure WAF policy portal | helps build and attach WAF policies and custom rules in a guided flow |
| Google Cloud Armor security policies | managed rule and custom-rule flow for edge and web protection |
Commercial or hosted accelerators worth knowing
Use these when you need scale, governance, or collaboration features that go beyond point tools.
| Platform | Strongest use case | Notes |
|---|---|---|
| 42Crunch | API contract security, audit, and testing workflows | strong when API security needs design-time governance |
| Snyk | developer-facing SCA, container, and IaC workflows | good when teams want integrated remediation guidance |
| Prisma Cloud / Bridgecrew | cloud + IaC posture and policy workflows | useful for broader cloud-security operating models |
| Datree | Kubernetes policy governance and admission workflows | good when teams want centralized policy and guardrails |
| Komodor / ValidKube | quick manifest debugging and validation | ValidKube itself stays a handy free front door |
Real UI examples — commercial or managed workflow views
42Crunch Platform — landing and navigation model
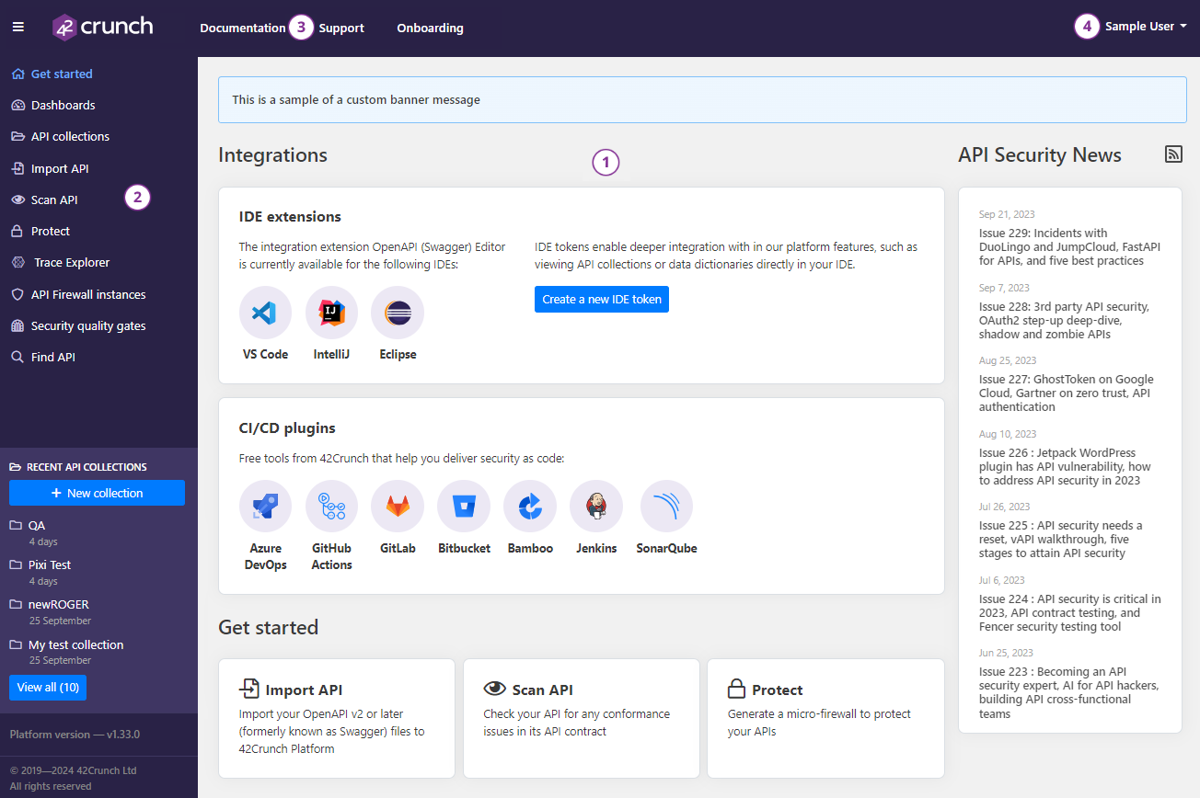
Public documentation screenshot of the 42Crunch platform landing page. It is a good visual example of a design-time API-security platform that combines collections, scanning, protection, and quality gates into one operating surface.
42Crunch IDE workflow — API audit feedback inside VS Code
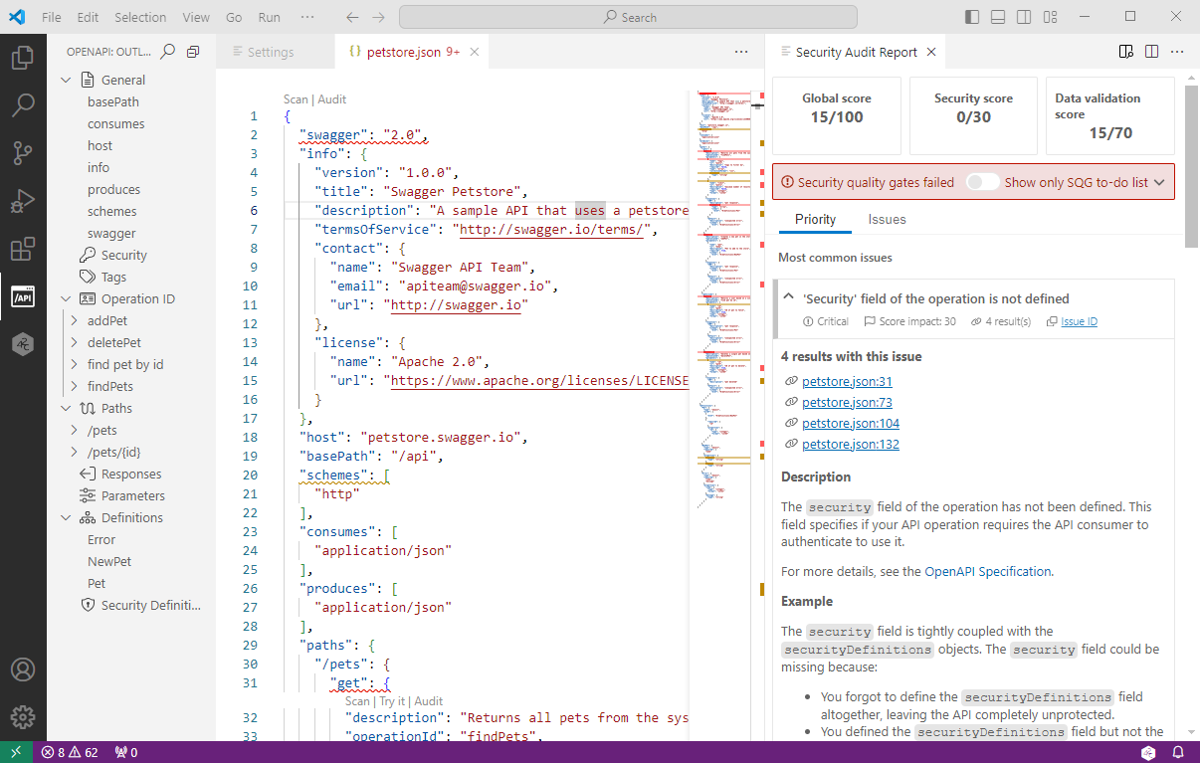
Public documentation screenshot of 42Crunch audit results inside VS Code. This is exactly the kind of in-workflow feedback loop that separates “platform only” tooling from developer-facing API security programs.
Fast decision guide
When you have an API spec
Start with:
- Swagger Editor or a local OpenAPI validator for quick syntax validation.
- Redocly CLI or Spectral for repeatable linting and standards.
- A richer API-security platform only if you need governance, audit, or collaboration at scale.
When you have Kubernetes YAML
Start with:
- ValidKube or Kubeconform for fast validation.
- Polaris for best-practice signal.
- Network Policy Editor, Kyverno Playground, or OPA Playground when you need policy authoring help.
When you have Docker or IaC
Start with:
- Hadolint for Dockerfiles.
- Checkov and/or Trivy for IaC and image-related checks.
- Provider-native GUIs when the change is really a cloud-policy authoring task, not a repo-linting task.
When you have headers, tokens, or browser security questions
Start with:
- CSP Evaluator for CSP.
- MDN Observatory or SecurityHeaders for public-site header checks.
- jwt.io for JWT structure and signature sanity checks.
Practical workflow pattern
A good pattern looks like this:
- prototype in a browser or visual editor;
- rewrite or codify the result in Git;
- add local validation;
- add CI enforcement;
- document the exception path when enforcement cannot be universal yet.
That pattern gives you speed and durability.
Companion pages in this KB
- API Definition Conformance Lab — OpenAPI, Contract Linting, AuthZ Checks, and CI Validation
- Terraform Security Scanning and Checkov
- Dockerfile Security Best Practices
- Network Policy Patterns
- OPA and Policy Enforcement
- Product Security Tooling Landscape and Inventory
Public references
- https://www.yamllint.com/
- https://jsonlint.com/
- https://editor.swagger.io/
- https://validkube.com/
- https://editor.networkpolicy.io/
- https://playground.kyverno.io/
- https://play.openpolicyagent.org/
- https://play.falco.org/
- https://csp-evaluator.withgoogle.com/
- https://developer.mozilla.org/en-US/observatory
- https://securityheaders.com/
- https://www.jwt.io/
- https://mermaid.live/
- https://github.com/hadolint/hadolint
- https://redocly.com/docs/cli
- https://stoplight.io/open-source/spectral
- https://github.com/bridgecrewio/checkov
- https://github.com/yannh/kubeconform
- https://github.com/FairwindsOps/polaris
- https://trivy.dev/
- https://docs.aws.amazon.com/IAM/latest/UserGuide/access_policies_create-console.html
- https://docs.aws.amazon.com/IAM/latest/UserGuide/access-analyzer-policy-generation.html
- https://docs.aws.amazon.com/waf/
- https://learn.microsoft.com/en-us/azure/web-application-firewall/ag/create-waf-policy-ag
- https://docs.cloud.google.com/armor/docs/security-policy-overview
---Author attribution: Ivan Piskunov, 2026 - Educational and defensive-engineering use.